
A newly discovered Linux malware dubbed 'DISGOMOJI' uses the novel approach of utilizing emojis to execute commands on infected devices in attacks on government agencies in India.
The malware was discovered by cybersecurity firm Volexity, which believes it is linked to a Pakistan-based threat actor known as 'UTA0137.'
"In 2024, Volexity identified a cyber-espionage campaign undertaken by a suspected Pakistan-based threat actor that Volexity currently tracks under the alias UTA0137," explains Volexity.
"Volexity assesses with high confidence that UTA0137 has espionage-related objectives and a remit to target government entities in India. Based on Volexity's analysis, UTA0137's campaigns appear to have been successful," continued the researchers.
The malware is similar to many other backdoors/botnets used in different attacks, allowing threat actors to execute commands, take screenshots, steal files, deploy additional payloads, and search for files.
However, its use of Discord and emojis as a command and control (C2) platform makes the malware stand out from others and could allow it to bypass security software that looks for text-based commands.
Discord and emojis as a C2
According to Volexity, the malware was discovered after the researchers spotted a UPX-packed ELF executable in a ZIP archive, likely distributed through phishing emails.
Volexity believes that the malware targets a custom Linux distribution named BOSS that Indian government agencies use as their desktop. However, the malware could just as easily be used in attacks against other Linux distributions.
When executed, the malware will download and display a PDF lure that is a beneficiary form from India's Defence Service Officer Provident Fund in case of an officer's death.
However, additional payloads will be downloaded in the background, including the DISGOMOJI malware and a shell script named 'uevent_seqnum.sh' that is used to search for USB drives and steal data from them.
When DISGOMOJI is launched, the malware will exfiltrate system information from the machine, including IP address, username, hostname, operating system, and the current working directory, which is sent back to the attackers.
To control the malware, the threat actors utilize the open-source command and control project discord-c2, which uses Discord and emojis to communicate with infected devices and execute commands.
The malware will connect to an attacker-controlled Discord server and wait for the threat actors to type emojis into the channel.
"DISGOMOJI listens for new messages in the command channel on the Discord server. C2 communication takes place using an emoji-based protocol where the attacker sends commands to the malware by sending emojis to the command channel, with additional parameters following the emoji where applicable. While DISGOMOJI is processing a command, it reacts with a “Clock” emoji in the command message to let the attacker know the command is being processed. Once the command is fully processed, the “Clock” emoji reaction is removed and DISGOMOJI adds a “Check Mark Button” emoji as a reaction to the command message to confirm the command was executed."
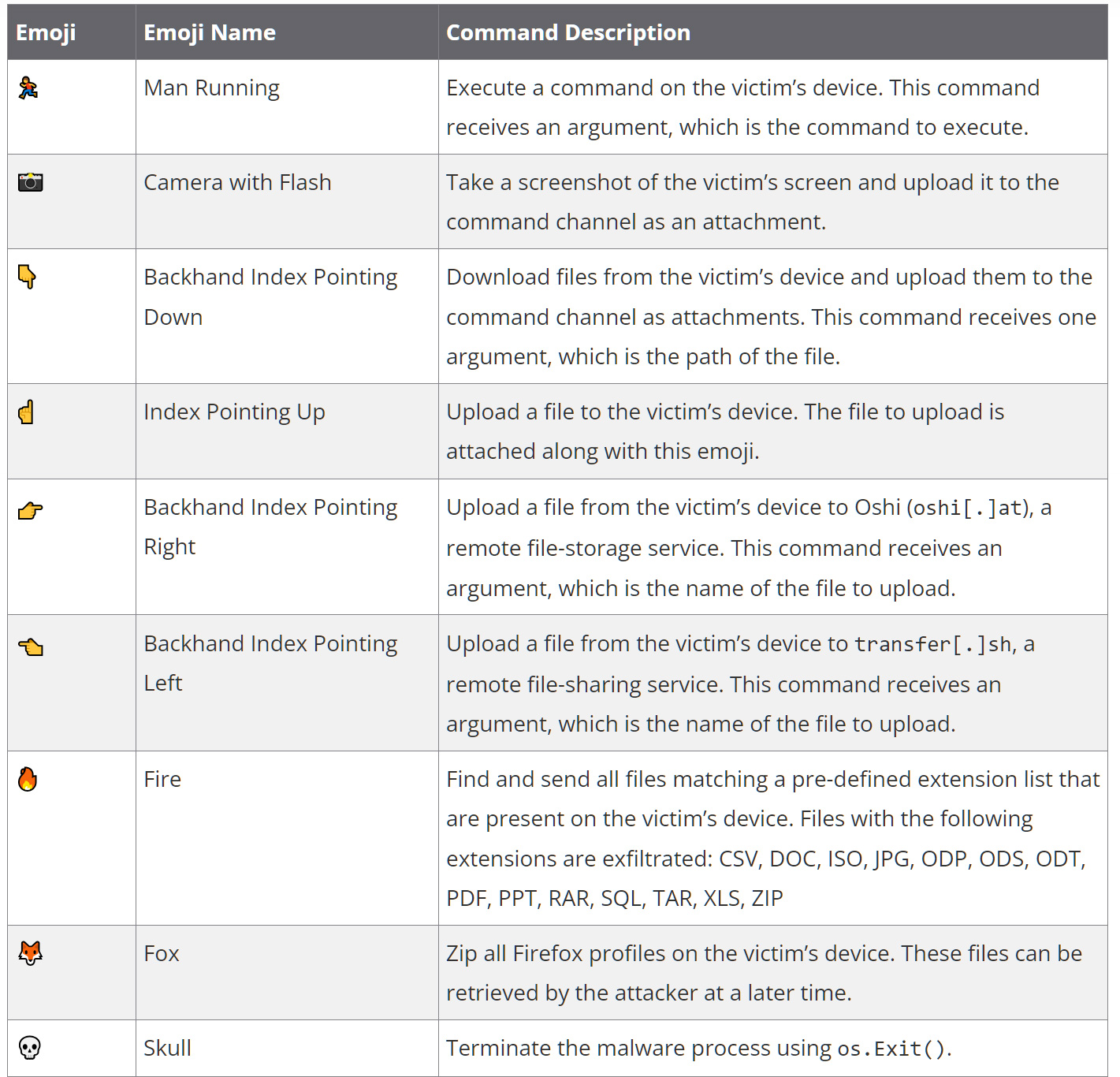
❖ VolexityNine emojis are used to represent commands to execute on an infected device, which are listed below.
The malware maintains persistence on the Linux device by using the @reboot cron command to execute the malware on boot.
Volexity says they discovered additional versions that utilized other persistence mechanisms for DISGOMOJI and the USB data theft script, including XDG autostart entries.
Once a device is breached, the threat actors utilize their access to spread laterally, steal data, and attempt to steal additional credentials from targeted users.
While emojis may seem like a "cute" novelty to the malware, they could allow it to bypass detection by security software that commonly looks for string-based malware commands, making this an interesting approach.



Post a Comment Community Rules
You need to login in order to post a comment
Not a member yet? Register Now