In an ongoing Kubernetes cryptomining campaign, attackers target OpenMetadata workloads using critical remote code execution and authentication vulnerabilities.
OpenMetadata is an open-source metadata management platform that helps data engineers and scientists to catalog and discover data assets within their organization, including databases, tables, files, and services.
The security vulnerabilities exploited in these attacks (CVE-2024-28255, CVE-2024-28847, CVE-2024-28253, CVE-2024-28848, and CVE-2024-28254) were reported on December 14 by GitHub Security Lab's Alvaro Muñoz and patched on January 5 in OpenMetadata versions 1.2.4 and newer.
According to Collate CTO and OpenMetadata project maintainer Sriharsha Chintalapani, these flaws "could allow non-authenticated, non-administrative users to inject malicious payloads and bypass security policies, potentially leading to privilege escalation."
Microsoft, which first spotted the attacks, says the five flaws have been actively exploited since early April to hijack Internet-exposed OpenMedata workloads left unpatched.
"Once they identify a vulnerable version of the application, the attackers exploit the mentioned vulnerabilities to gain code execution on the container running the vulnerable OpenMetadata image," Microsoft threat intel researchers Hagai Ran Kestenberg and Yossi Weizman said.
"Once the attackers confirm their access and validate connectivity, they proceed to download the payload, a cryptomining-related malware, from a remote server. We observed the attackers using a remote server located in China."
The server hosting the malware payloads also contains additional cryptomining malware for both Linux and Windows platforms.
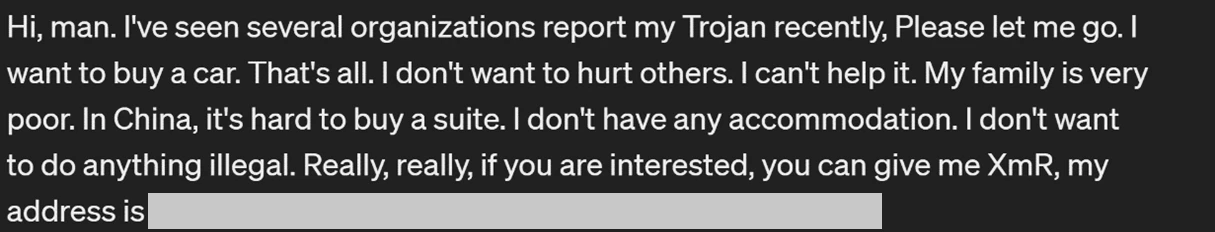
The attackers will also leave a note on compromised systems, asking the victims to donate Monero cryptocurrency to help them buy a car or a "suite" in China.
In the next stage, they remove the initial payloads from the hijacked Kubernetes app and establish a reverse shell connection using the Netcat tool. This grants them remote access to the container, allowing them to take control of the system.
Moreover, to maintain persistent access, the attackers use cronjobs to schedule tasks executing malicious code at predetermined intervals.
Admins who have to expose their OpenMedata workloads online are advised to change the default credentials and ensure that their apps are patched against recently disclosed vulnerabilities at all times.
To get a list of all OpenMetadata workloads running in your Kubernetes environment, you can use the following command:
kubectl get pods --all-namespaces -o=jsonpath='{range .items[*]}{.spec.containers[*].image}{"\n"}{end}' | grep 'openmetadata'
"This attack serves as a valuable reminder of why it's crucial to stay compliant and run fully patched workloads in containerized environments," Kestenberg and Weizman concluded.
Update April 22, 16:07 EDT: Added more disclosure and patching timeline details.



Post a Comment Community Rules
You need to login in order to post a comment
Not a member yet? Register Now