A new wave of attacks by the DarkGate malware operation exploits a now-fixed Windows Defender SmartScreen vulnerability to bypass security checks and automatically install fake software installers.
SmartScreen is a Windows security feature that displays a warning when users attempt to run unrecognized or suspicious files downloaded from the internet.
The flaw tracked as CVE-2024-21412 is a Windows Defender SmartScreen flaw that allows specially crafted downloaded files to bypass these security warnings.
Attackers can exploit the flaw by creating a Windows Internet shortcut (.url file) that points to another .url file hosted on a remote SMB share, which would cause the file at the final location to be executed automatically.
Microsoft fixed the flaw in mid-February, with Trend Micro disclosing that the financially motivated Water Hydra hacking group previously exploited it as a zero-day to drop their DarkMe malware onto traders' systems.
Today, Trend Micro analysts reported that DarkGate operators are exploiting the same flaw to improve their chances of success (infection) on targeted systems.
This is a significant development for the malware, which, together with Pikabot, has filled the void created by QBot's disruption last summer and is used by multiple cybercriminals for malware distribution.
DarkGate attack details
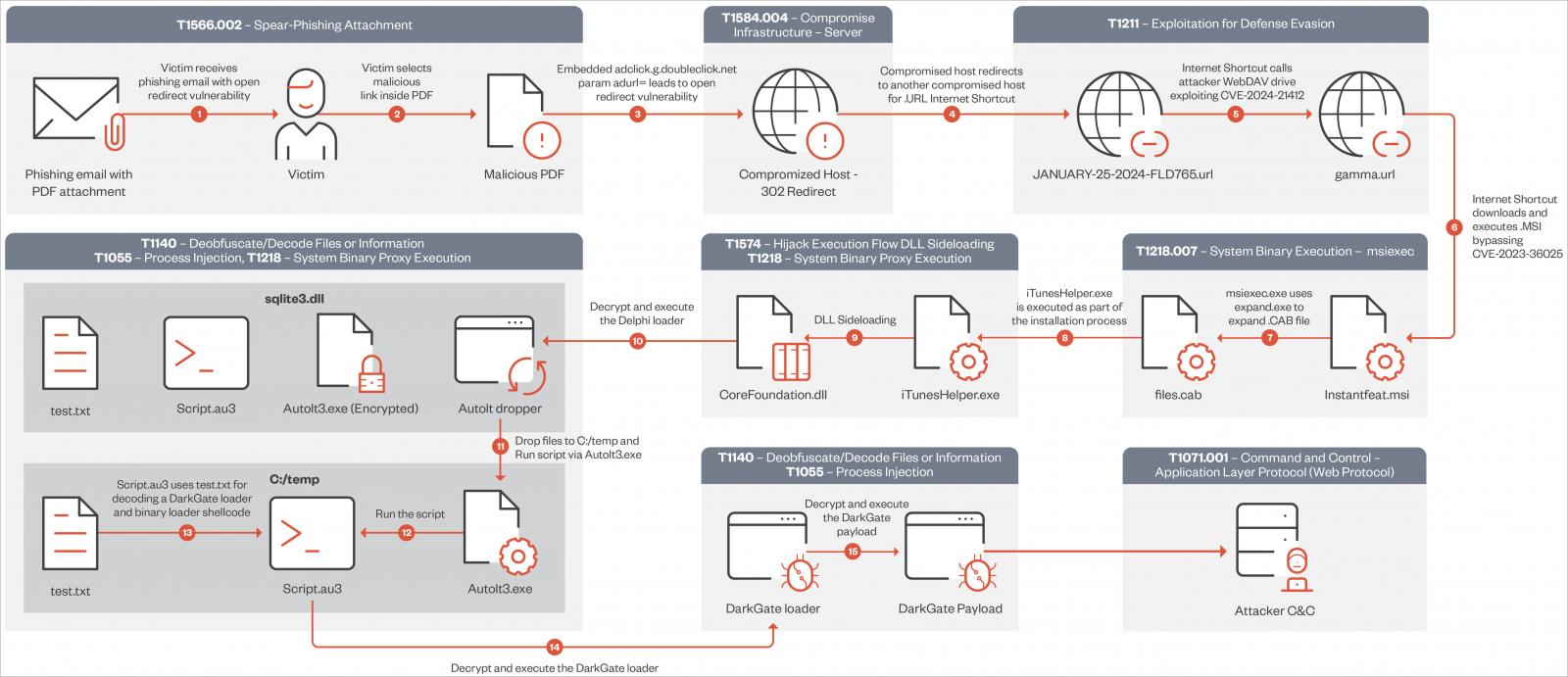
The attack begins with a malicious email that includes a PDF attachment with links that utilize open redirects from Google DoubleClick Digital Marketing (DDM) services to bypass email security checks.
When a victim clicks on the link, they are redirected to a compromised web server that hosts an internet shortcut file. This shortcut file (.url) links to a second shortcut file hosted on an attacker-controlled WebDAV server.
Source: Trend Micro
Using one Windows Shortcut to open a second Shortcut on a remote server effectively exploits the CVE-2024-21412 flaw, causing a malicious MSI file to execute automatically on the device.
Source: Trend Micro
These MSI files masqueraded as legitimate software from NVIDIA, the Apple iTunes app, or Notion.
Upon execution of the MSI installer, another DLL sideloading flaw involving the "libcef.dll" file and a loader named "sqlite3.dll" will decrypt and execute the DarkGate malware payload on the system.
Once it's initialized, the malware can steal data, fetch additional payloads and inject them into running processes, perform key logging, and give attackers real-time remote access.
The complex and multi-step infection chain employed by DarkGate operators since mid-January 2024 is summarized in the below diagram:
Source: Trend Micro
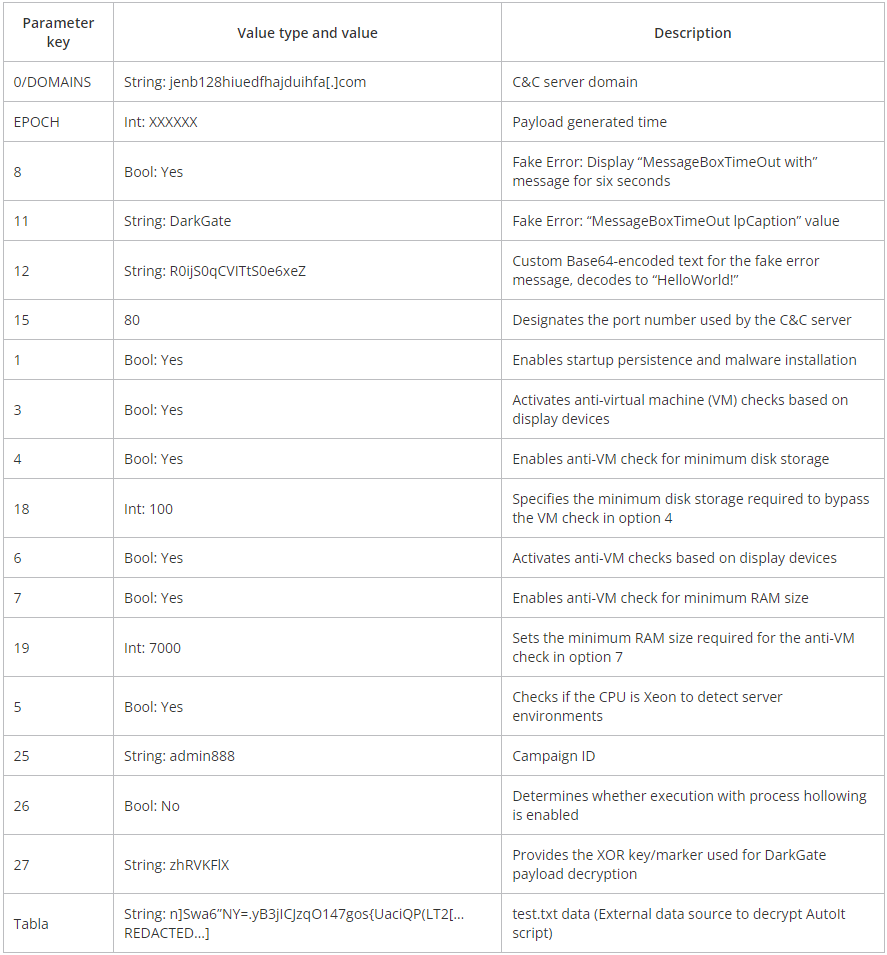
Trend Micro says this campaign employs DarkGate version 6.1.7, which, compared to the older version 5, features XOR-encrypted configuration, new config options, and updates on the command and control (C2) values.
The configuration parameters available in DarkGate 6 enable its operators to determine various operational tactics and evasion techniques, such as enabling startup persistence or specifying minimum disk storage and RAM size to evade analysis environments.
Source: Trend Micro
The first step to mitigate the risk from these attacks would be to apply Microsoft's February 2024 Patch Tuesday update, which fixes CVE-2024-21412.
Trend Micro has published the complete list of the indicators of compromise (IoCs) for this DarkGate campaign on this webpage.



Comments
DyingCrow - 3 months ago
We all know what happens when we download teams from the official page and run it LOL
electrolite - 3 months ago
Why in the world would an internet shortcut file pointing to remote msi ever be allowed to execute immediately in the first place? Internet shortcut files should be restricted to web pages only, that was the original intent of such files, wasn't it? The way windows handles .url is very cryptic. There is no file association for .url so you cannot even set it to open with a browser instead (where it would at least prompt the user or just download the file and not execute it right away).