Security researchers have demonstrated a method to decrypt proprietary firmware images embedded in D-Link routers.
Firmware is the piece of code that powers low-level functions on hardware devices. It is typically hard-coded within the read-only memory.
Companies encrypt firmware images in their devices to prevent their reverse engineering by competitors and threat actors, and to prevent their customers (or better yet malware) from flashing the device with customized firmware.
“Manufacturers encrypt firmware generally to try to keep people from analyzing the binaries therein. Also, if done correctly, encrypting firmware images can prevent unauthorized, modified firmware images from being able to be flashed on a device,” security researcher Nick Starke explained in an interview with BleepingComputer.
To decrypt anything, one would either need the secret decryption key or a means to break the encryption algorithm. If the firmware images are indeed encrypted, how could have they been so easily deciphered?
Analyzing D-Links encrypted firmware image
At the beginning of his analysis, Starke had downloaded the latest version of the D-Link firmware (1.11B02) from their support website and proceeded to use Binwalk to analyze it.
Binwalk is a simple reverse engineering utility specifically designed for firmware extraction and analysis.
To the researcher's surprise, Binwalk revealed nothing:
Source: Nick Starke's blog
The result was an immediate indication that the firmware was encrypted.
Interestingly, unzipping an older "1.02B03" version obtained from the same D-Link support site revealed two firmware files:
DIR3040A1_FW102B03.binDIR3040A1_FW102B03_uncrypted.bin
The presence of a binary ending in "..._uncrypted.bin" was an immediate indication that it's potentially unencrypted, while the other was likely encrypted.
Running binwalk on "DIR3040A1_FW102B03_uncrypted.bin" revealed a handful of useful information:
Source: Nick Starke's blog
The above information told the researchers that the image contained an unencrypted firmware binary that they could then extract and analyze for stored decryption keys.
"Bingo, a uImage header, and accompanying filesystem. We can extract this using binwalk -eM DIR3040A1_FW102B03_uncrypted.bin. Looking at the filesystem, the first thing I did is look for certificates," explains Starke in his blog post.
Keys embedded in older firmware
After further analysis, his suspicions were correct, and both the decryption and encryption keys were found embedded in the binary.

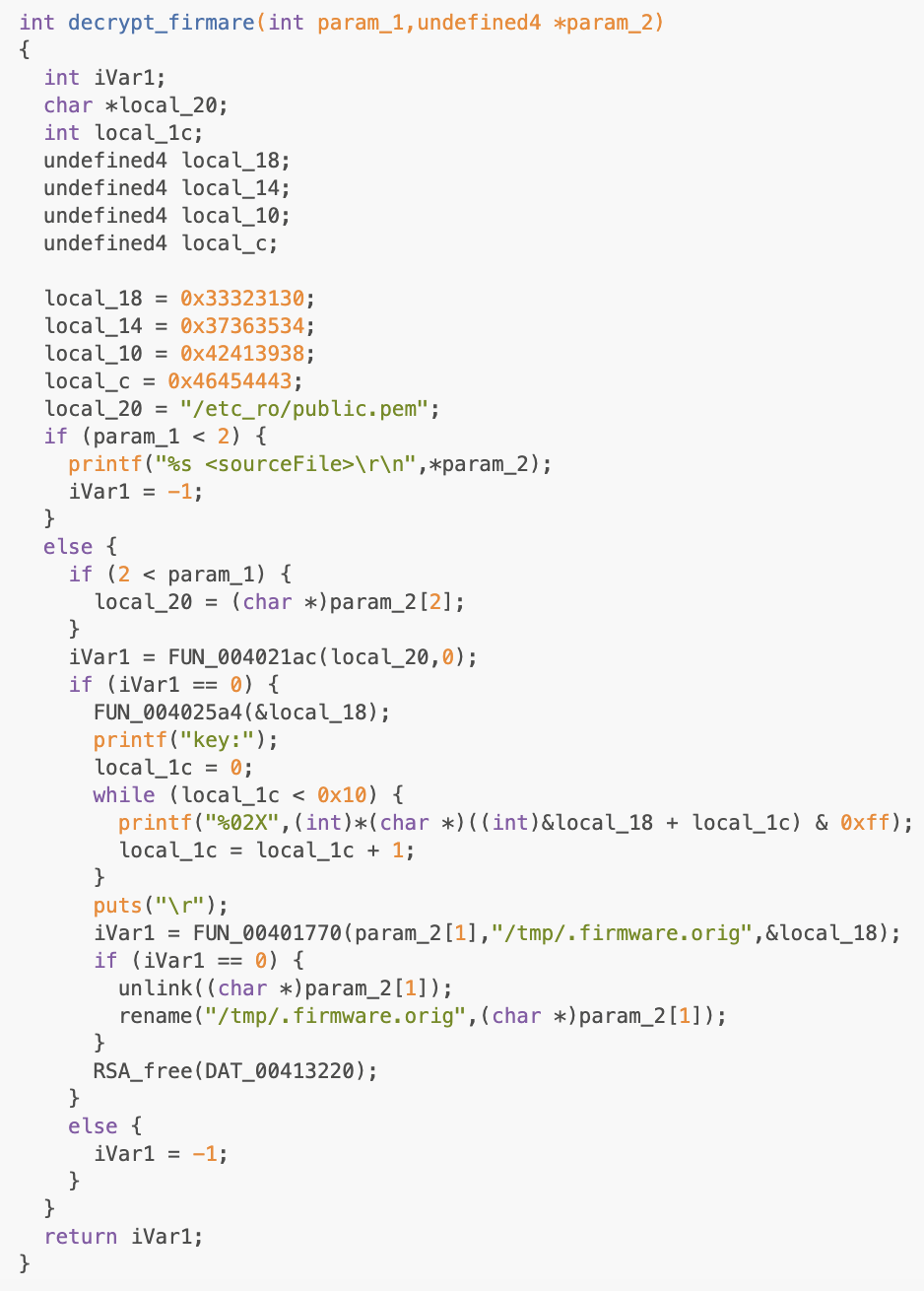
In addition to the key and certificate files, a program called /bin/imgdecrypt was also present, which is the decryption tool for encrypted images.
This decryption tool, though, has one caveat, as Starke explains:
"There is some sort of key derived from the local stack variables, that is not straightforward to reverse. So instead of spending hours trying to figure out exactly what the code that produces the key does, why don't we just try to run the binary passing it our firmware image we want to decrypt?"
After taking a series of steps, the researcher was able to stage the environment to sufficiently enable decryption of the latest 1.11B02 firmware version.
Running the imgdecrypt binary against the encrypted firmware image revealed the secret key: C05FBF1936C99429CE2A0781F08D6AD8
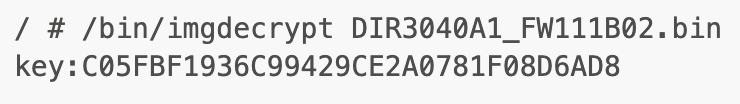
"Not only does it output the key to decrypt the firmware file image, but it also places the decrypted version in /tmp/.firmware.orig," read the blog post.
This means a reverse engineer could now proceed to analyze the firmware image which had been otherwise encrypted.
“More and more device manufacturers are moving toward encrypting firmware, however, most are starting from unencrypted firmware images. This usually means there must be an unencrypted firmware image with the password or key stored inside of it. If you can find the last unencrypted image, you can generally find the password and thus decrypt any subsequent encrypted images,” Starke further told BleepingComputer.
The same technique has been used earlier this month by another security researcher Rick Sanchez who did an in-depth static analysis of the decryption algorithm in a multi-part blog post.
Sanchez, who had initially discovered this flaw, relied on purchasing a physical D-Link device, which can cost up to $200, as explained in Part 1 of his post.
As the secret key remains the same for all encrypted firmware images (on any device), obtaining an earlier image from a support site would achieve the same goal.
Both researchers discovered the flaw independently at different times, and there are clear differences in their research approaches and the tools used.
These findings stress how even the encryption is futile and turns into security through obscurity should there exist trivial means to obtain the key guarding the secret.
In D-Link's case, even the latest firmware images are open to curious researchers for analysis who can get their hands on older firmware images - from D-Link's site.



Comments
DLINKSIRT - 3 years ago
D-Link SIRT :: For Accurate and Up-to-Date information please go to: https://bit.ly/2OJYZvV
Zavorskiy - 3 years ago
Therefore, I do not buy routers from this company.
Sup3rus3r - 3 years ago
This is not such a big deal, this mean from closed source it became open source. Linux is open source and is much better than windows. Open source means more eyes can review the code so many things can be improved.
yawnshard - 3 years ago
Chinese people did this 2019 already: https://itw01.com/8BONHEY.html
All in this story of the security "researcher" is much exactly what the Chinese did.
Sorry, I don't see how he came up with it. Just google the key, look at the dates.
Even down to running binwalk at the end as well. All copied from the Chinese.