The new NoEscape ransomware operation is believed to be a rebrand of Avaddon, a ransomware gang that shut down and released its decryption keys in 2021.
NoEscape launched in June 2023 when it began targeting the enterprise in double-extortion attacks. As part of these attacks, the threat actors steal data and encrypt files on Windows, Linux, and VMware ESXi servers.
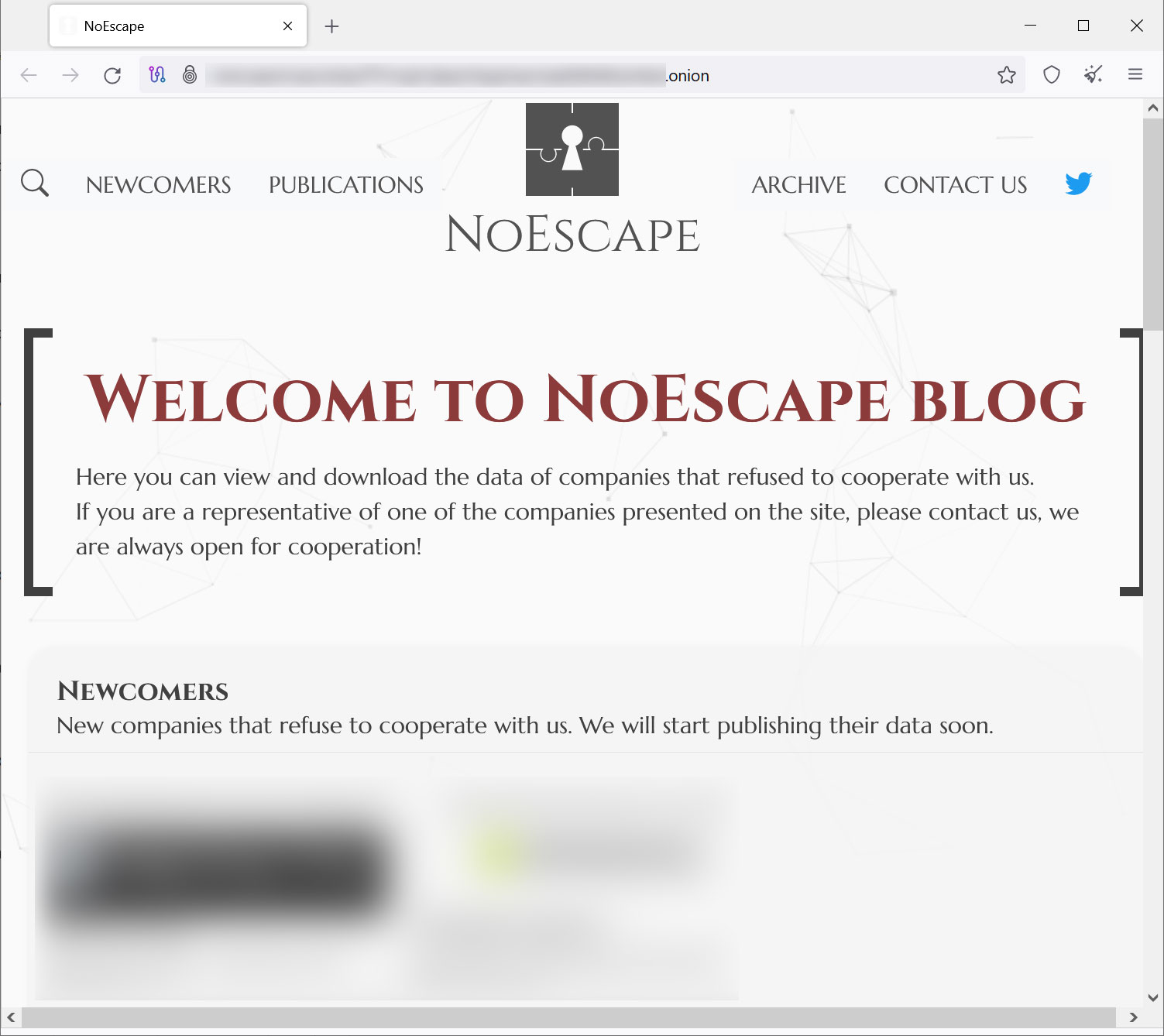
The threat actors then threaten to publicly release stolen data if a ransom is not paid. BleepingComputer is aware of NoEscape ransomware demands ranging between hundreds of thousands of dollars to over $10 million.
Like other ransomware gangs, NoEscape does not allow its members to target CIS (ex-Soviet Union) countries, with victims from those countries receiving free decryptors and information on how they were breached.
At this time, the ransomware gang has listed ten companies from different countries and industries on their data leak site, illustrating that they are not targeting a particular vertical.
An Avaddon rebrand
The Avaddon ransomware operation launched in June 2020 using phishing campaigns to target corporate victims.
However, in June 2021, a month after the FBI and Australian law enforcement released Avaddon advisories, the ransomware gang suddenly shut down its operation and shared victims' decryption keys with BleepingComputer in an anonymous tip.
Since then, there has not been any known ransomware or extortion activity associated with the threat actors until last month with the launch of the NoEscape ransomware operation.
ID-Ransomware creator and ransomware expert Michael Gillespie told BleepingComputer that NoEscape's and Avaddon's ransomware encryptors are almost identical, with only one notable change in encryption algorithms.
Previously, the Avaddon encryptor utilized AES for file encryption, with NoEscape switching to the Salsa20 algorithm.
Otherwise, the encryptors are virtually identical, with the encryption logic and file formats almost identical, including a unique way of "chunking of the RSA encrypted blobs."
Furthermore, BleepingComputer has determined that the Avaddon and NoEscape encryptors use the same configuration file and directives as described in this Mandiant article and outlined below.
{
"lck":
{
"lid": "",
"iv_key": "",
"mp_key": ""
},
"ext":
{
"ignore": [],
"full": []
},
"paths":
{
"skip": [],
"primary": []
},
"settings":
{
"build_type": "",
"add_to_autorun": ,
"interval": ,
"print_note": ,
"set_wallpaper": ,
"large_file_size_mb": ,
"spot_size_mb":
},
"kill_services": [],
"kill_processes": [],
"note_text": ""
}
While it is possible that the NoEscape threat actors purchased the source code of the encryptor from Avaddon, BleepingComputer has been told by numerous researchers that it is believed that some of the core Avaddon members are now part of the new ransomware operation.
The NoEscape encryptor
A sample of the NoEscape ransomware was shared with BleepingComputer so we could analyze it.
When executed, NoEscape will run the following commands to delete Windows Shadow Volume Copies, local Windows backup catalogs, and to turn off Windows automatic repair.
SHADOWCOPY DELETE /nointeractive
wmic SHADOWCOPY DELETE /nointeractive
wbadmin DELETE SYSTEMSTATEBACKUP -deleteOldest
wbadmin DELETE BACKUP -deleteOldest
wbadmin DELETE BACKUP -keepVersions:0
vssadmin Delete Shadows /All /Quiet
bcdedit /set {default} recoveryenabled No
The encryptor will then begin to terminate the following processes, including those associated with security software, backup applications, and web and database servers.
360doctor, 360se, Culture, Defwatch, GDscan, MsDtSrvr, QBCFMonitorService, QBDBMgr, QBIDPService, QBW32, RAgui, RTVscan, agntsvc, agntsvcencsvc, agntsvcisqlplussvc, anvir, anvir64, apache, axlbridge, backup, ccleaner, ccleaner64, dbeng50, dbsnmp, encsvc, excel, far, fdhost, fdlauncher, httpd, infopath, isqlplussvc, java, kingdee, msaccess, msftesql, mspub, mydesktopqos, mydesktopservice, mysqld-nt, mysqld-opt, mysqld, ncsvc, ocautoupds, ocomm, ocssd, onedrive, onenote, oracle, outlook, powerpnt, procexp, qbupdate, sqbcoreservice, sql, sqlagent, sqlbrowser, sqlmangr, sqlserver, sqlservr, sqlwriter, steam, supervise, synctime, taskkill, tasklist, tbirdconfig, thebat, thunderbird, tomcat, tomcat6, u8, ufida, visio, wdswfsafe, winword, wordpad, wuauclt, wxServer, wxServerView, and xfssvccon
It will also stop the following Windows services associated with databases, QuickBooks, security software, and virtual machine platforms.
Culserver, DefWatch, GxBlr, GxCIMgr, GxCVD, GxFWD, GxVss, QBCFMonitorService, QBIDPService, RTVscan, SavRoam, VMAuthdService, VMUSBArbService, VMnetDHCP, VMwareHostd, backup, ccEvtMgr, ccSetMgr, dbeng8, dbsrv12, memtas, mepocs, msexchange, msmdsrv, sophos, sql, sqladhlp, sqlagent, sqlbrowser, sqlservr, sqlwriter, svc$, tomcat6, veeam, vmware-converter, vmware-usbarbitator64, vss
The ransomware terminates these applications to unlock files that may be opened and prevented from being encrypted.
However, even if files are locked, the encryptor utilizes the Windows Restart Manager API to close processes or shut down Windows services that may keep a file open and prevent encryption.
When encrypting files, the encryptor will skip all files that have the following file extensions:
exe, bat, bin, cmd, com, cpl, dat, dll, drv, hta, ini, lnk, lock, log, mod, msc, msi, msp, pif, prf, rdp, scr, shs, swp, sys, theme
It will also skip files in folders whose names contain the following strings:
$recycle.bin, $windows.~bt, $windows.~ws, %PROGRAMFILES(x86)%, %PUBLIC%, %ProgramData%, %SYSTEMDRIVE%\\Program Files, %SYSTEMDRIVE%\\Users\\All Users, %SYSTEMDRIVE%\\Windows, %TMP%, %USERPROFILE%\\AppData, AppData, %AppData%, EFI, Intel, MSOCache, Mozilla, Program Files, ProgramData, Tor Browser, Windows, WINDOWS, boot, google, perflogs, system volume information, windows.old
During encryption, Gillespie told BleepingComputer that it could be configured to use three modes:
- Full - the entire file is encrypted
- Partial - Only the first X megabytes are encrypted.
- Chunked - Uses intermittent encryption to encrypt chunks of data.
However, NoEscape includes a configuration option that forces the encryptor to fully encrypt files with the accdb, edb, mdb, mdf, mds, ndf, and sql file extensions.
Files are encrypted using Salsa20, with the encryption key encrypted with a bundled RSA public key. Encrypted files will have a 10 character extension appended to the filename, which is unique for each victim, as illustrated below.
Source: BleepingComputer
The encryptor will also configure a scheduled task named 'SystemUpdate' for persistence on the device and to launch the encryptor when logging into Windows.
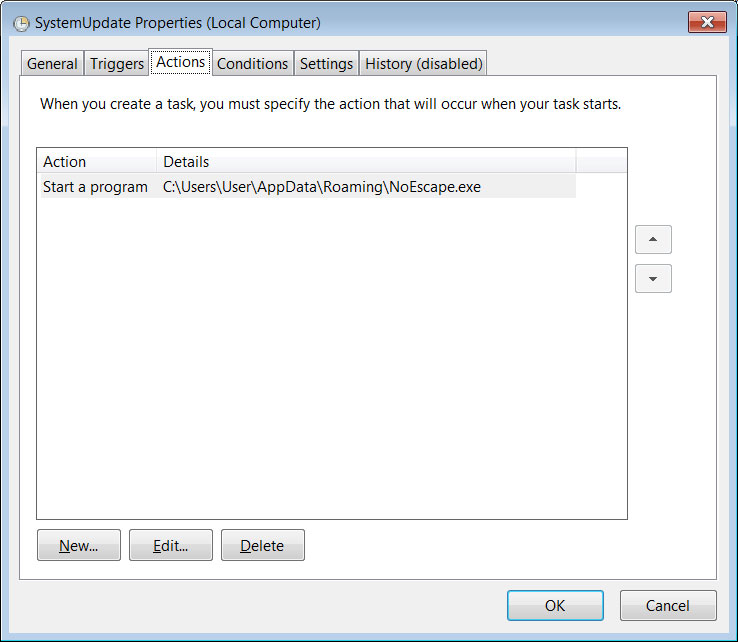
Source: BleepingComputer
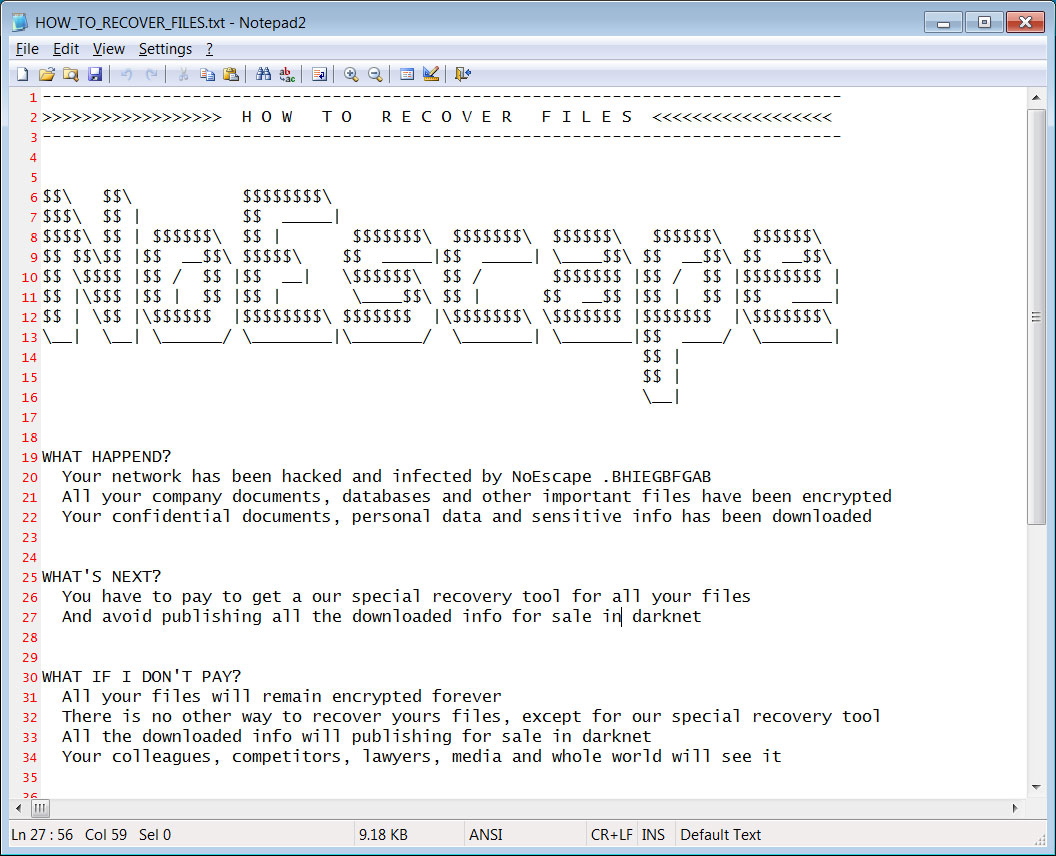
The ransomware will also change the Windows wallpaper to an image telling victims they can find instructions in the ransom notes named HOW_TO_RECOVER_FILES.txt.

Source: BleepingComputer
The HOW_TO_RECOVER_FILES.txt ransom notes are located in each folder on the device and include information on what happened to a victim's files and links to the NoEscape Tor negotiation site.
"We are not a politically company and we are not interested in your private affairs. We are a commercial company, and we are only interested in money," promises the NoEscape ransom note.
Source: BleepingComputer
On Linux, the /etc/motd is also replaced with the ransom note, which is displayed to victims when they log in.
The ransom notes contain a "personal ID" required to log in to the threat actor's Tor payment site and access the victim's unique negotiation page. This page includes the ransom amount in bitcoins, a test decryption feature, and a chat panel to negotiate with the threat actors.
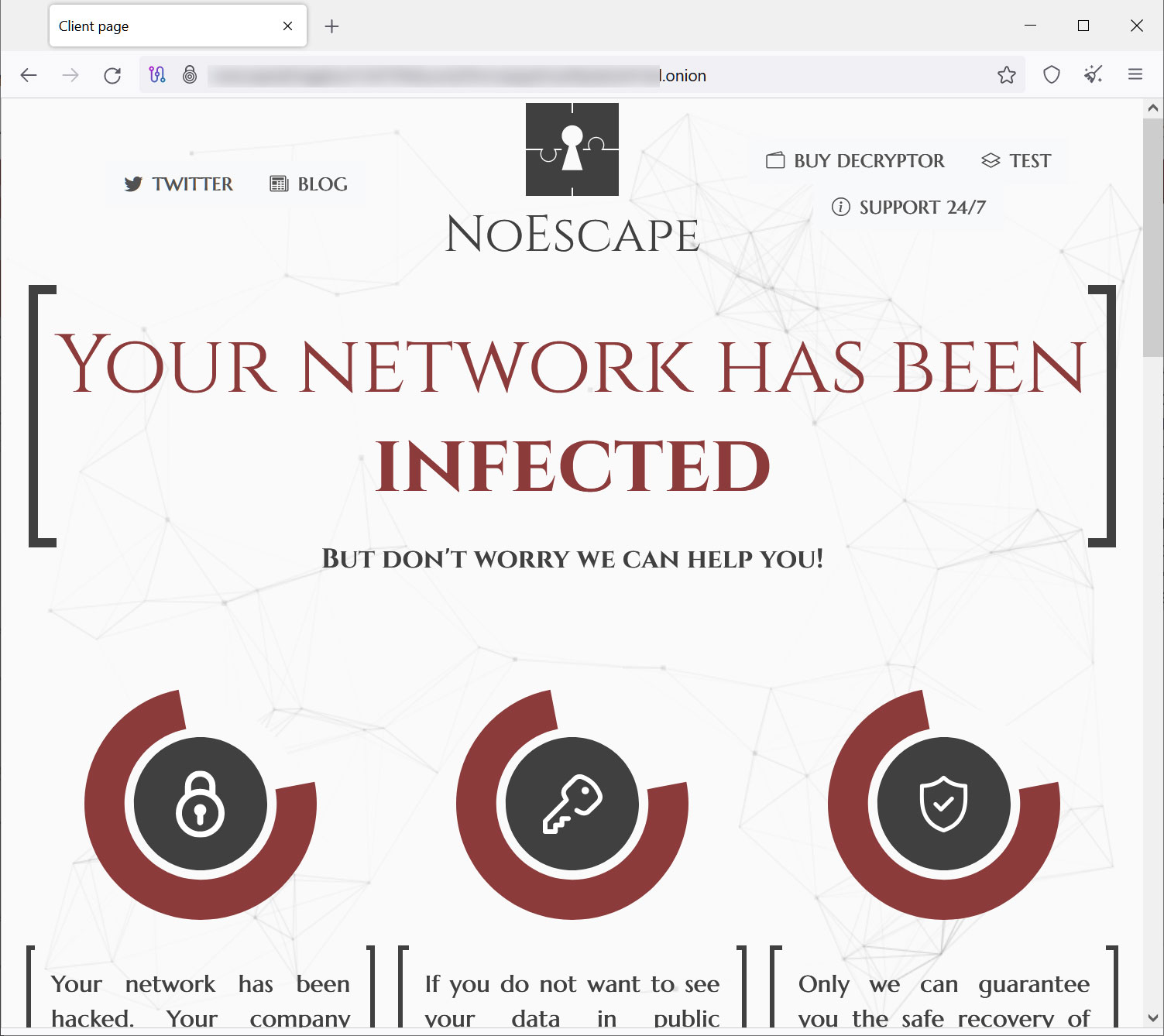
Source: BleepingComputer
As previously said, BleepingComputer has seen NoEscape ransom demands ranging from a few hundred thousand dollars to over $10 million.
After paying, victims will be shown a list of available decryptors, which are those for Windows XP, modern versions of Windows, and Linux.
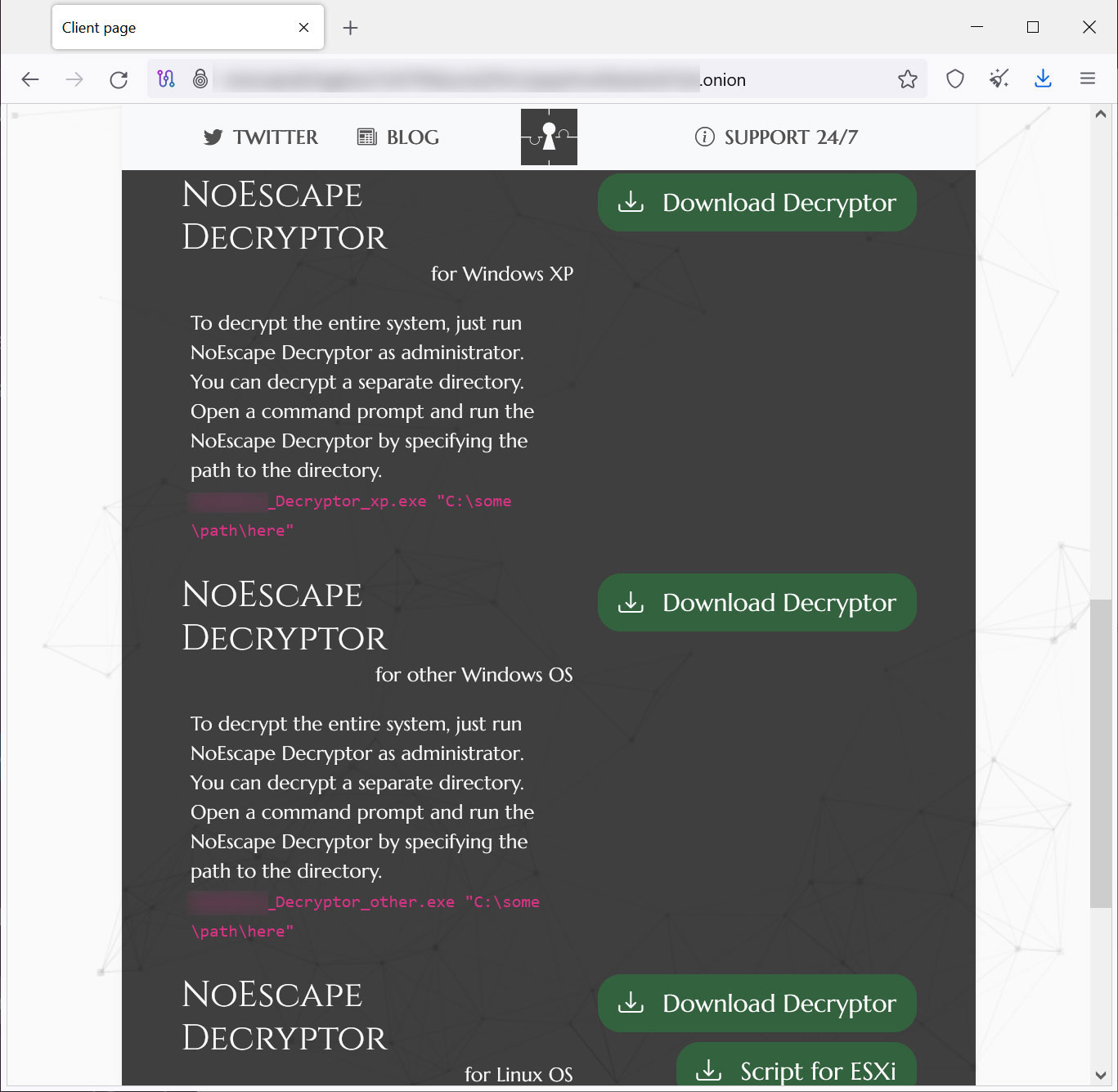
Source: BleepingComputer
For enterprise victims running VMware ESXi, NoEscape provides a shell script that can be used to restore the /etc/motd and decrypt files using the Linux decryptor.
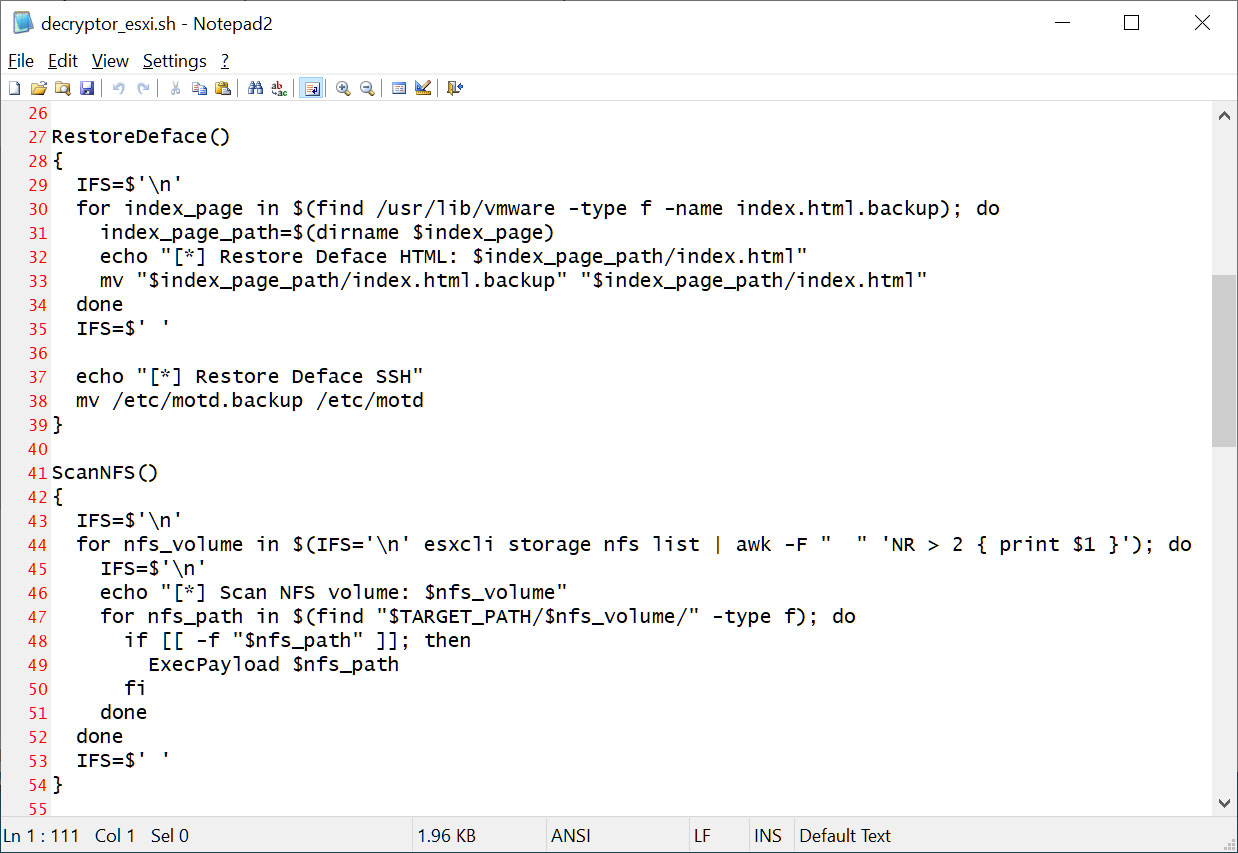
Source: BleepingComputer
Data leak site used to extort victims
Like other ransomware operations, NoEscape will breach a corporate network and spread laterally to other devices. Once the threat actors gain Windows domain admin credentials, they will deploy the ransomware throughout the network.
However, before encrypting files, the threat actors have already stolen corporate data to be used as leverage in their extortion attempts. The threat actors then warn victims that their data will be publicly released or sold to other threat actors if a ransom is not paid.
At the time of this writing, NoEscape had leaked the data or begun extorting ten victims on their data leak site, with the size of leaked data ranging from 3.7 GB for one company to 111 GB for another.
Source: BleepingComputer
The ransomware is currently being analyzed for weaknesses, and BleepingComputer does not advise paying a ransom until it's determined if a free decryptor can recover files for free.



Post a Comment Community Rules
You need to login in order to post a comment
Not a member yet? Register Now