A ransomware attack that hit pathology services provider Synnovis on Monday and impacted several major NHS hospitals in London has now been linked to the Qilin ransomware operation.
Ciaran Martin, the inaugural CEO of the UK's National Cyber Security Centre (NCSC), said today that the Qilin gang is likely responsible for the incident
The attack has resulted in Synnovis being locked out of its systems and is causing ongoing service disruptions at Guy's and St Thomas' NHS Foundation Trust, King's College Hospital NHS Foundation Trust, and various primary care providers across south east London.
"We believe it is a Russian group of cyber criminals who call themselves Qilin," Martin told BBC Radio 4 on Wednesday.
"They're simply looking for money. It's unlikely they would have known that they would have caused such serious primary healthcare disruption when they set out to attack the company."
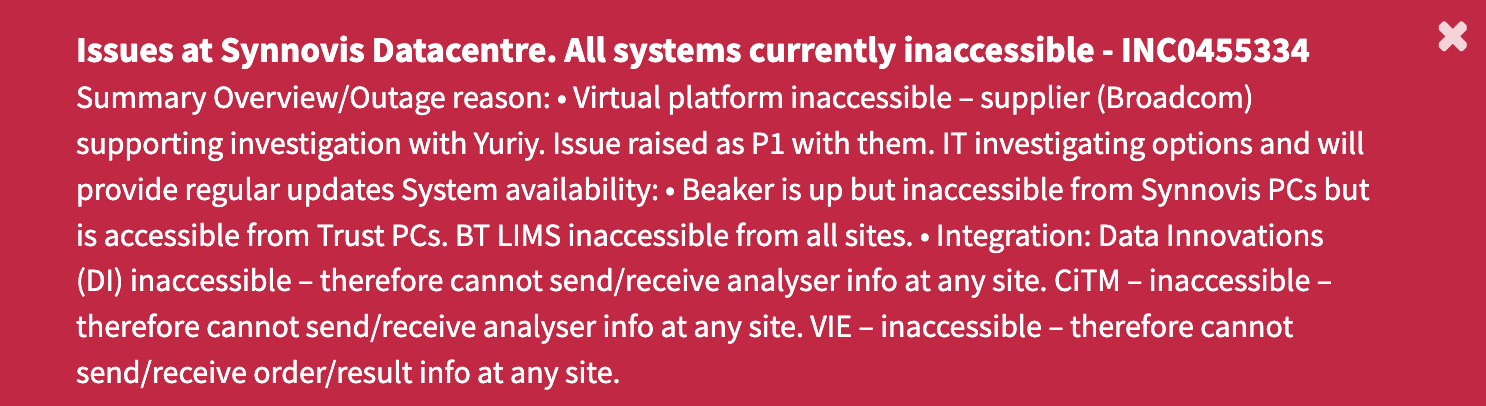
An alert on Synnovis' customer service portal currently warns of data center issues and that all systems are currently inaccessible.
Memos sent by officials of hospitals affected by the Synnovis ransomware attack revealed on Tuesday that this "ongoing critical incident" has had a "major impact" on their procedures and operations.
Some non-emergency pathology appointments, blood transfusions, and surgeries at the impacted London hospitals have been either postponed, canceled, or redirected to other providers.
The NHS said on Wednesday that urgent and emergency services like A&E, urgent care centers, and maternity departments are open as usual. An NHS England cyber incident response team is currently assessing the full extent of the attack and its impact on patient and employee data.
"All urgent and emergency services remain open as usual and the majority of outpatient services continue to operate as normal," an NHS spokesperson said today.
"Unfortunately, some operations and procedures which rely more heavily on pathology services have been postponed, and blood testing is being prioritised for the most urgent cases, meaning some patients have had phlebotomy appointments cancelled."
Qilin's dark web leak site is currently down, although there is no evidence that this outage is linked to the ransomware attack that hit Synnovis' systems on Monday, June 3.
The Qilin ransomware operation surfaced in August 2022 under the "Agenda" name but was rebranded as Qilin one month later.
The gang has been linked to or claimed a steady stream of victims since its launch, with over 130 companies added to its dark web leak site over the last two years. However, Qilin operators haven't been very active until attacks picked up towards the end of 2023.
Since December 2023, these cybercriminals have also been developing one of the most advanced and customizable Linux encryptors seen to date, specifically designed to target VMware ESXi virtual machines favored by enterprise organizations for their light resource needs.
Similar to other ransomware gangs targeting businesses, Qilin operates by infiltrating a company's networks and extracting data while moving through the victim's systems.
After obtaining admin credentials for the servers and collecting all sensitive data, the attackers deploy the ransomware payloads to encrypt all devices connected to the network.
They then leverage the stolen data and the encrypted files to carry out double-extortion attacks, pressuring the targeted companies to meet their demands. So far, BleepingComputer has seen ransom demands ranging from $25,000 to millions of dollars, depending on the victim's size.



Post a Comment Community Rules
You need to login in order to post a comment
Not a member yet? Register Now