A recently spotted malvertising campaign tricked users with an in-browser Windows update simulation to deliver the Aurora information stealing malware.
Written in Golang, Aurora has been available on various hacker forums for more than a year, advertised as an info stealer with extensive capabilities and low antivirus detection.
According to researchers at Malwarebytes, the malvertising operation relies on popunder ads on adult content websites with high-traffic adult content and redirects potential victims to a malware-serving location.
Not a Windows update
Popunder ads are cheap ‘pop-up’ ads that launch behind the active browser window, staying hidden from the user until they close or move the main browser window.
In December last year, Google reported that popunders were used in an ad fraud campaign that amassed hundreds of thousands of visitors and tens of millions of fraudulent ad impressions.
The more recent one spotted by Malwarebytes has a much lower impact, with close to 30,000 users redirected and almost 600 downloaded and installed the data-stealing malware on their systems.
However, the threat actor came up with an imaginative idea where the popunder renders a full-screen browser window that simulates a Windows system update screen.
The researchers tracked more than a dozen domains used in the campaigns, many of them appearing to impersonate adult websites, that simulated the fake Windows update:
- activessd[.]ru
- chistauyavoda[.]ru
- xxxxxxxxxxxxxxx[.]ru
- activehdd[.]ru
- oled8kultra[.]ru
- xhamster-18[.]ru
- oled8kultra[.]site
- activessd6[.]ru
- activedebian[.]ru
- shluhapizdec[.]ru
- 04042023[.]ru
- clickaineasdfer[.]ru
- moskovpizda[.]ru
- pochelvpizdy[.]ru
- evatds[.]ru
- click7adilla[.]ru
- grhfgetraeg6yrt[.]site
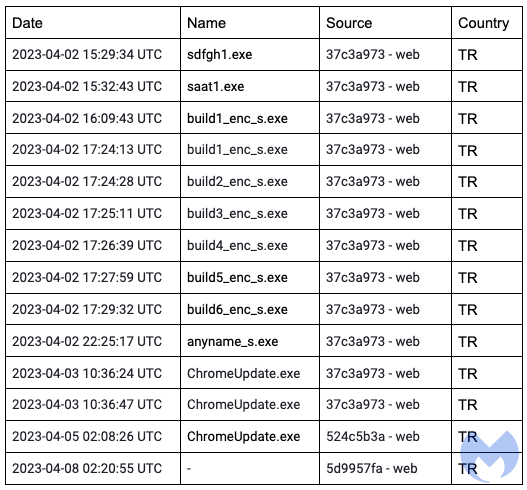
All of them served for download a file named "ChromeUpdate.exe," revealing the deception of the full-screen browser screen; however, some users were still tricked into deploying the malicious executable.
New malware loader
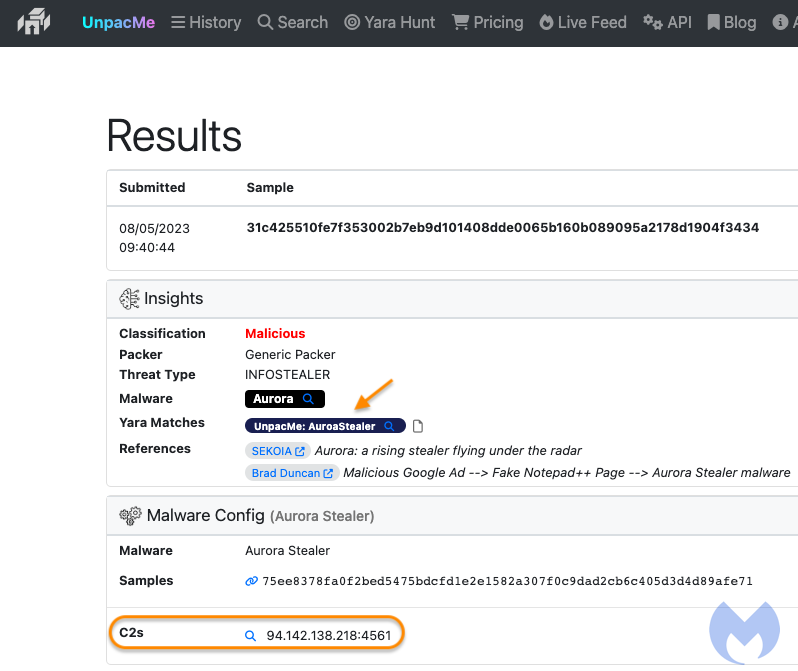
The alleged Chrome updater is a so called “fully undetectable” (FUD) malware loader called ‘Invalid Printer’ that seems to be used exclusively by this particular threat actor.
Malwarebytes says that when its analysts discovered ‘Invalid Printer,’ no antivirus engines on Virus Total flagged it as malicious. Detection started to pick up a few weeks later, though, following the publication of a relevant report from Morphisec.
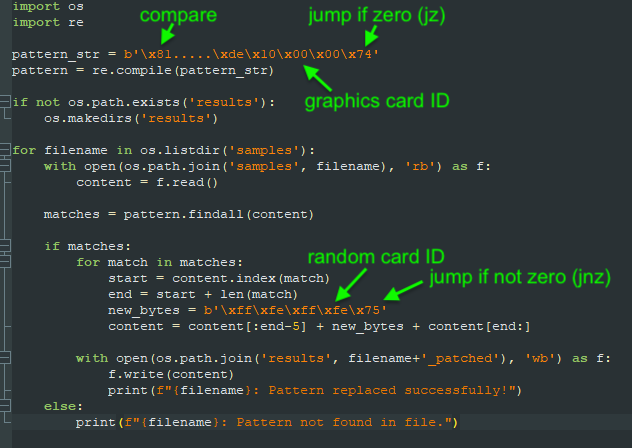
Invalid Printer first checks the host’s graphic card to determine if it’s running on a virtual machine or in a sandbox environment. If it's not, it unpacks and launches a copy of the Aurora information stealer, the researchers found.
Malwarebytes comments that the threat actor behind this campaign appears to be particularly interested in creating hard-to-detect tools, and they are constantly uploading new samples on Virus Total to check how they fare against detection engines.
Jérôme Segura, director of threat intelligence at Malwarebytes, noticed that every time a new sample was first submitted to Virus Total it came from a user in Turkey and that "in many instances the file name looked like it had come fresh from the compiler (i.e. build1_enc_s.exe)."
Further investigation revealed that the threat actor also uses an Amadey panel, potentially indicating the use of the well-documented reconnaissance and malware loading tool, and also runs tech support scams targeting Ukrainians.
Malwarebytes provides a technical analysis of the malware installation and behavior along with a set of indicators of compromise that companies and security vendors can use to defend their users.



Comments
Cauthon - 1 year ago
Thanks. It is encouraging that we can depend on our friends at Malwarebytes to catch the difficult ones. I guess I should run that more often :-)