A new destructive malware named AcidPour was spotted in the wild, featuring data-wiper functionality and targeting Linux x86 IoT and networking devices.
Data wipers are a category of malware designed for destructive attacks that delete files and data on targeted devices. This type of malware is commonly used to disrupt an organization's operations for political reasons or as a distraction from a larger attack.
The new malware spotted by SentinelLabs' security researcher Tom Hegel, AcidPour, is considered a variant of the AcidRain data wiper.
AcidRain is a data wiping malware designed to erase files on routers and modems. The malware was utilized in a cyberattack against satellite communications provider Viasat, which impacted service availability across Ukraine and Europe.
AcidPour was uploaded from Ukraine on March 16, 2024, which complicates tracing its operators, as AcidRain was used against the country in the past.
A thread on X by Juan Andrés Guerrero Saade provides some details about the new variant, though it is unknown whether it has been used in any attacks in the wild and who its targets might have been.
The AcidPour wiper
AcidPour shares many similarities with AcidRain, such as targeting specific directories and device paths common in embedded Linux distributions, but their codebase overlaps by an estimated 30%.
This indicates either significant evolution or possibly a different origin. Guerrero Saade says it's not unlikely that a different group of attackers replicated some of AcidRain's functionality.
AcidPour shares input/output control (IOCTL)-based wiping logic with VPNFilter's 'dstr' plugin and AcidRain, indicating a continuation or adaptation of the previously documented malicious techniques.
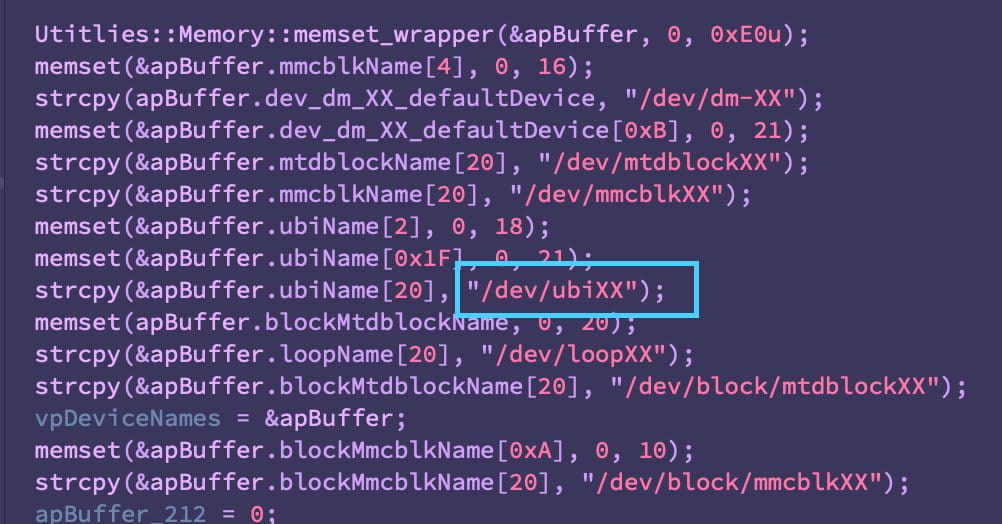
The new malware includes references to '/dev/ubiXX' indicating a focus on embedded systems using flash memory.
There is also a reference to and '/dev/dm-XX', which are virtual block devices associated with Logical Volume Management (LVM), respectively. Network Attached Storage devices, including QNAP and Synology, utilize LVM to manage RAID arrays.
These additions suggest that AcidPour might target a broader range of devices or systems than its predecessor, which targeted the more specific MIPS architecture.
The SentinelLabs analyst publicly shared the malware's hash and called on the security research community to participate in collaborative analysis and verification, as the targets and distribution volume are currently unknown. A sample can be found on VirusTotal.
These additions suggest that AcidPour might target a broader range of devices or systems than its predecessor, which targeted the more specific MIPS architecture.
"This is a threat to watch. My concern is elevated because this variant is a more powerful AcidRain variant, covering more hardware and operating system types," warned Rob Joyce, the NSA's Director of Cybersecurity.
Update 3/21: SentinelLabs has now published a detailed report on AcidPour on its website.



Post a Comment Community Rules
You need to login in order to post a comment
Not a member yet? Register Now