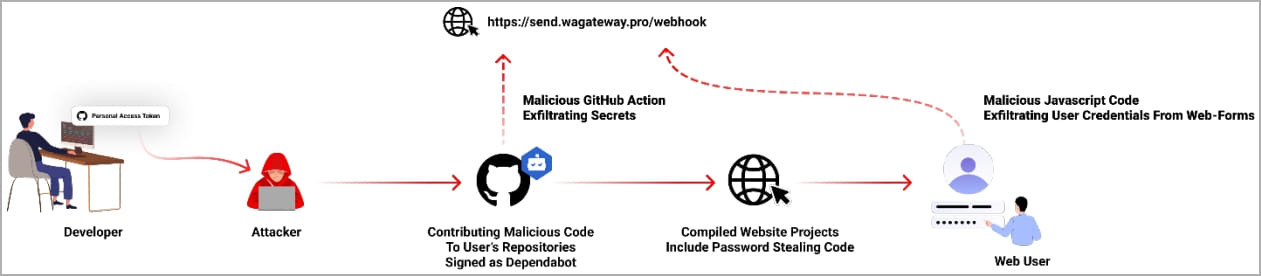
Hackers are breaching GitHub accounts and inserting malicious code disguised as Dependabot contributions to steal authentication secrets and passwords from developers.
The campaign unfolded in July 2023, when researchers discovered unusual commits on hundreds of public and private repositories forged to appear as Dependabot commits.
Dependabot is an automated tool provided by GitHub that scans projects for vulnerable dependencies and then automatically issues pull requests to install the updated versions.
As reported today by Checkmarx, these fake Dependabot contributions were made possible using stolen GitHub access tokens with the attackers' goal of injecting malicious code to steal the project's secrets.
Impersonating GitHub's Dependabot
The attack began with the attackers somehow obtaining their targets' personal GitHub access tokens, which Checkmarx has no insight into.
The threat actors then appear to be using automated scripts to create fake commit messages titled "fix" that appear to be by the user account "dependabot[bot]."
These commits introduce malicious code into the project that performs the following two actions:
- Extract secrets from the targeted GitHub project and send them to the attacker's command and control server.
- Modify existing JavaScript files in the breached repository to add malware that steals passwords from web-form submissions and sends them to the same C2 address.
The secrets exfiltration is achieved by adding the GitHub action file "hook.yml" as a new workflow triggered on every code push event on the impacted repository.
The password-stealer component injects obfuscated JavaScript into the end of all JavaScript (.js) files that load the following script from a remote site. This script will monitor for form submissions to steal passwords from any form inputs of type 'password.'
As many compromised tokens also granted access to private repositories, the attack affected both public and private GitHub repositories.
Possible compromise points
Checkmarx's analysts examined the logs from some victims and found that their accounts were compromised using stolen PATs (personal access tokens).
These tokens are stored locally on the developer's computers and can be used to log in to GitHub without going through 2FA (two-factor authentication) steps.
"Sadly, the token's access log activity is not visible in the account's audit log. So if you're token got compromised, you can't know for sure because the access logs are missing," warns Checkmarx
Although the cybersecurity firm didn't reach a concrete conclusion on the exact means by which the attackers stole these tokens, they assume it might be through a malware infection possibly introduced to the developer's device via a malicious package.
Most compromised users are from Indonesia, implying a targeted attack tailored to this demographic. However, the available evidence doesn't provide specific details about the theme.
A proposed measure to defend against these attacks is to switch to GitHub's fine-grained personal access tokens, which limits each user to specific permissions, hence reducing risks in case of compromise.



Post a Comment Community Rules
You need to login in order to post a comment
Not a member yet? Register Now