Several state and key industrial organizations in Russia were attacked with a custom Go-based backdoor that performs data theft, likely aiding espionage operations.
Kaspersky first detected the campaign in June 2023, while in mid-August, the cybersecurity firm spotted a newer version of the backdoor that introduced better evasion, indicating ongoing optimization of the attacks.
The threat actors responsible for this campaign are unknown, and Kaspersky was limited to sharing indicators of compromise that can help defenders thwart the attacks.
Malicious ARJ archives
The attack begins with an email carrying a malicious ARJ archive named 'finansovyy_kontrol_2023_180529.rar' (financial control), which is a Nullsoft archive executable.
The archive contains a decoy PDF document used for distracting the victim and an NSIS script that fetches the primary payload from an external URL address (fas-gov-ru[.]com) and launches it.
The malware payload is dropped at 'C:\ProgramData\Microsoft\DeviceSync\' as 'UsrRunVGA.exe.'
Source: Kaspersky
Kaspersky says the same phishing wave distributed two more backdoors named 'Netrunner' and 'Dmcserv.' These are the same malware with different C2 (command and control) server configurations.
The script launches the malicious executables in a hidden window and adds a Start Menu link to establish persistence.
Source: Kaspersky
The functionality of the backdoor includes the following:
- List files and folders in a specified directory.
- Transfer (exfiltrate) files from the host to the C2.
- Obtain clipboard contents.
- Grab desktop screenshots.
- Search disk for files of specific extensions (.doc, .docx, .pdf, .xls, .xlsx, .ppt, .pptx, .zip, .rar, .7z, .odt, .ods, .kdbx, .ovpn, .pem, .crt, .key) and transfer them to the C2.
All data sent to the C2 server is first AES encrypted to evade detection from network monitoring solutions.
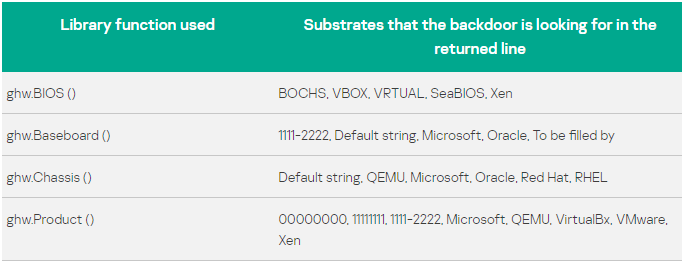
To evade analysis, the malware performs username, system name, and directory checks to detect if it's running in a virtualized environment and exits if it does.
The results of these checks are sent to the C2 in the initial phase of the infection to be used for victim profiling.
Source: Kaspersky
New version steals passwords
In mid-August, Kaspersky noticed a new variant of the backdoor that featured minor changes like the removal of some noisy preliminary checks and the addition of new file-stealing capabilities.
Most notably, the new version adds a module that targets user passwords stored in 27 web browsers and the Thunderbird email client.
Browsers targeted by the latest backdoor version include Chrome, Firefox, Edge, Opera, Brave, Vivaldi, and Yandex, a popular and trusted browser in Russia.
The AES key has been refreshed in this malware version, and RSA asymmetric encryption has been added to protect client-C2 command and parameter communications.



Post a Comment Community Rules
You need to login in order to post a comment
Not a member yet? Register Now